Executive summary
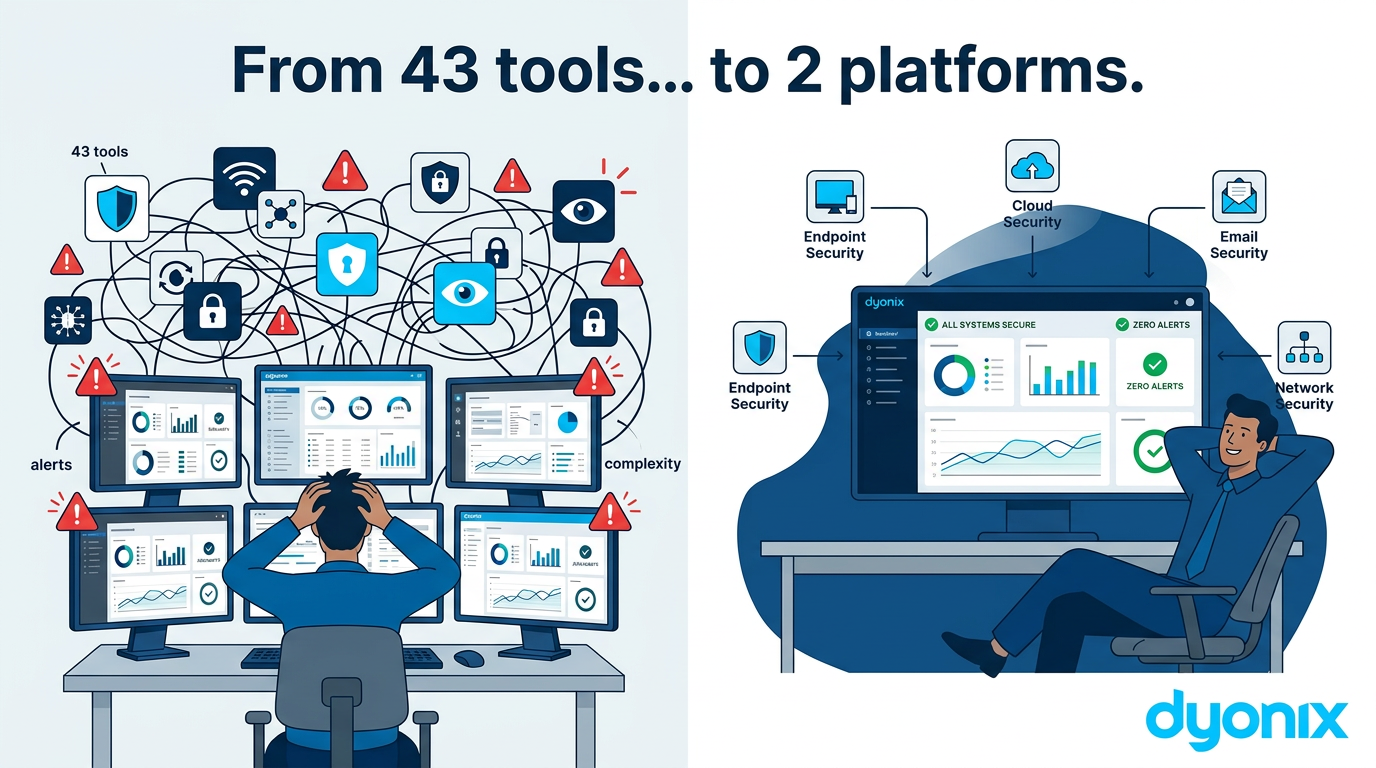
Most organisations now run dozens of overlapping security tools. On average, enterprises operate around 43 different security solutions across prevention, detection, response, and compliance. This tool sprawl creates complexity, blinds teams to real risk, and makes it harder – not easier – to prevent breaches. Consolidating onto a small number of integrated platforms is one of the most effective ways to regain control, reduce time-to-detect and time-to-contain, and lower the real cost of staying secure.
Introduction
Over the last decade, every new threat category seemed to come with its own must-have product. Cloud security? Buy a cloud security tool. Ransomware? Add an EDR product. Shadow IT? Another discovery tool. The result is familiar to most security and IT leaders: a growing zoo of agents, licences, dashboards, and alert queues.
Recent industry research shows that organisations now run an average of 43 separate security solutions. Each tool may be valuable in isolation, but together they form a highly complex system that is difficult to manage, monitor, and tune. That complexity directly impacts how quickly teams can understand what is happening in their environment and respond when something goes wrong.
The expanding attack surface
At the same time, the attack surface continues to grow. Organisations are consuming more cloud services, adopting SaaS at scale, enabling remote and hybrid work, connecting OT and IoT devices, and relying on increasingly complex supply chains. Every new application, identity, and integration is another way for attackers to get in – or to move laterally once they are inside.
Data from recent breach investigations paints a clear picture of how multi-dimensional modern risk has become:
- A significant share of breaches involve humans – from social engineering and phishing to errors and misconfigurations.
- Many breaches still exploit known vulnerabilities in systems and applications that could, at least in theory, have been patched.
- A sizeable proportion of incidents abuse legitimate installed tools already inside the environment, such as remote access or administration utilities.
- Most breaches involve at least one third party somewhere in the attack chain, such as a supplier, service provider, or other external partner.
In other words, risk does not just come from “the bad guys out there”. It flows through your people, your partners, your configurations, and even the legitimate tools you depend on to run the business.

When more tools becomes more risk
On paper, a best-of-breed stack of dozens of products looks comprehensive. In practice, it often introduces more risk than it removes. Security leaders now consistently cite complexity as the single biggest impediment to effective cybersecurity operations.
Each additional tool adds:
- Another console and data model to learn and maintain.
- More policies, rules, and detection content to create and keep in sync.
- More alerts to triage and manually correlate with signals from elsewhere.
- Another integration to maintain with your SIEM, ticketing, or SOAR platform.
This is especially painful for lean IT and security teams, who rarely have the headcount to specialise in every niche product. The more tools you add, the more time your people spend reconciling dashboards and fighting integration fires rather than actually improving security posture.
Industry data also shows that organisations with more mature, integrated security programmes are faster at identifying and containing incidents, and see a lower percentage of incidents turning into full data breaches. Larger organisations that invest in strong, coherent security programmes experience materially fewer breaches relative to incident volume than less mature peers.

Why consolidating to platforms works
The alternative to tool sprawl is a platform-first approach. Instead of buying a separate product for every problem, you standardise on a small number of powerful platforms that cover the complete attack lifecycle across the major parts of your environment.
A GravityZone-class XDR platform is a good example of this approach. From a single console, it can align controls, telemetry, and response across:
- Endpoints and servers.
- Identities and authentication.
- Cloud workloads and containers.
- Email and collaboration platforms.
- Network and perimeter visibility.
Because these capabilities are designed to work together from the start, you get consistent policies, shared context, and correlated detection out of the box. Telemetry from multiple domains feeds into a unified analytics layer, and automated playbooks can see and act across the entire environment. This reduces mean time to detect, investigate, and contain incidents, while also lowering total cost of ownership compared with running many disconnected point products.
What the data tells us
- Organisations run an average of 43 separate security solutions.
- Security leaders now rank complexity as the top impediment to effective cybersecurity operations.
- A significant portion of breaches involve human factors, from misconfigurations to successful social engineering.
- Many breaches still exploit known vulnerabilities in systems and applications that could have been patched.
- A sizeable share of incidents use legitimate installed tools to move and act inside the network.
- Most breaches involve at least one third party somewhere in the attack chain.
- Organisations with higher security platform maturity are measurably faster at identifying and containing incidents, reducing breach impact and cost.
How Dyonix helps you go from 43 to 2
At Dyonix, we work with organisations that are tired of juggling dozens of tools and still not feeling secure. Our focus is on designing and running lean, outcome-driven security architectures based on a small number of integrated platforms rather than an ever-growing zoo of products.
We typically anchor this around two core platforms:
- A GravityZone-class XDR platform for endpoints, identities, cloud workloads, email, and servers.
- FortiGate next-generation firewalls for network and perimeter security.
Together, these give you unified visibility and control across the places attackers actually move, without needing 30–40 separate tools to get there.
Why FortiGate is our second core platform
The “2” in our “43 to 2” approach is not just about XDR on endpoints, identities, and workloads. The second pillar is network security, where FortiGate next-generation firewalls give us deep, policy-driven control over how traffic moves inside and outside your environment. This becomes critical wherever you operate on shared or untrusted networks.
Think about a hotel, co-working space, clinic, or hospitality venue offering guest Wi‑Fi. You are effectively inviting hundreds or thousands of unmanaged devices onto the same physical infrastructure as your business systems. Without strong network segmentation, inspection, and access control, a single compromised guest device can become a launchpad to probe the rest of your network.
By standardising on FortiGate, we can:
- Segment guest, staff, and critical business networks so traffic is strictly contained.
- Enforce application-aware policies instead of relying only on basic port rules.
- Inspect traffic for threats, command‑and‑control, and known bad destinations in real time.
- Apply consistent security policies across branches, data centres, and cloud edges.
- Integrate network telemetry and events into the same detection and response workflows as your XDR platform.
For environments like hotels and shared offices, this means you can confidently offer guest connectivity without exposing your core systems. For distributed businesses, it means your branch offices, remote sites, and cloud edges are protected by the same, centrally managed policy as your headquarters.
Together, GravityZone for endpoints, identities, cloud, email and FortiGate for network and perimeter give you the “two platforms” that replace dozens of overlapping point products while actually improving control and visibility.
The Dyonix Security Stack Consolidation Assessment
To make the first step easy, we offer a structured Security Stack Consolidation Assessment. In a short engagement, we:
- Inventory your existing tools, mapped against the attack lifecycle and your critical assets.
- Highlight redundancy, blind spots, and integration gaps that are increasing risk and cost.
- Model a consolidated “43 to 2” target architecture aligned to your business and compliance needs.
- Provide a phased roadmap for migration that respects current investments and operational realities.
You walk away with a clear picture of where complexity is costing you – and a concrete plan to move towards a simpler, more effective security posture.
Conclusion
The evidence is clear: tool sprawl and complexity have become core cybersecurity problems in their own right. With an average of 43 security tools in play and humans, vulnerabilities, legitimate tools, and third parties all contributing to breaches, simply buying more point products is not a sustainable strategy.
Consolidating onto a small number of powerful platforms is how leading organisations regain visibility, reduce time-to-detect and time-to-contain, and lower the true cost of staying secure. If you are ready to move from “more tools” to “better outcomes”, Dyonix can help you design and deliver that journey.
Ready to see what consolidation could look like in your environment? Get in touch with us to schedule your Security Stack Consolidation Assessment.
